In Azure when we think of network security we can think of NSG’s (Network Security Groups). These groups are really similar to a firewall. They sit right in front of the VM you want it to and contains a set of security rules for allowing or denying traffic. Below is an NSG and it will look very familiar to those with a networking background.

You’ll see we have this idea of inbound and outbound security rules.Note that the RDP rule has a priority of 300. This means that it has priority over other rules.
I have a VM in North Europe sitting behind the NSG above.

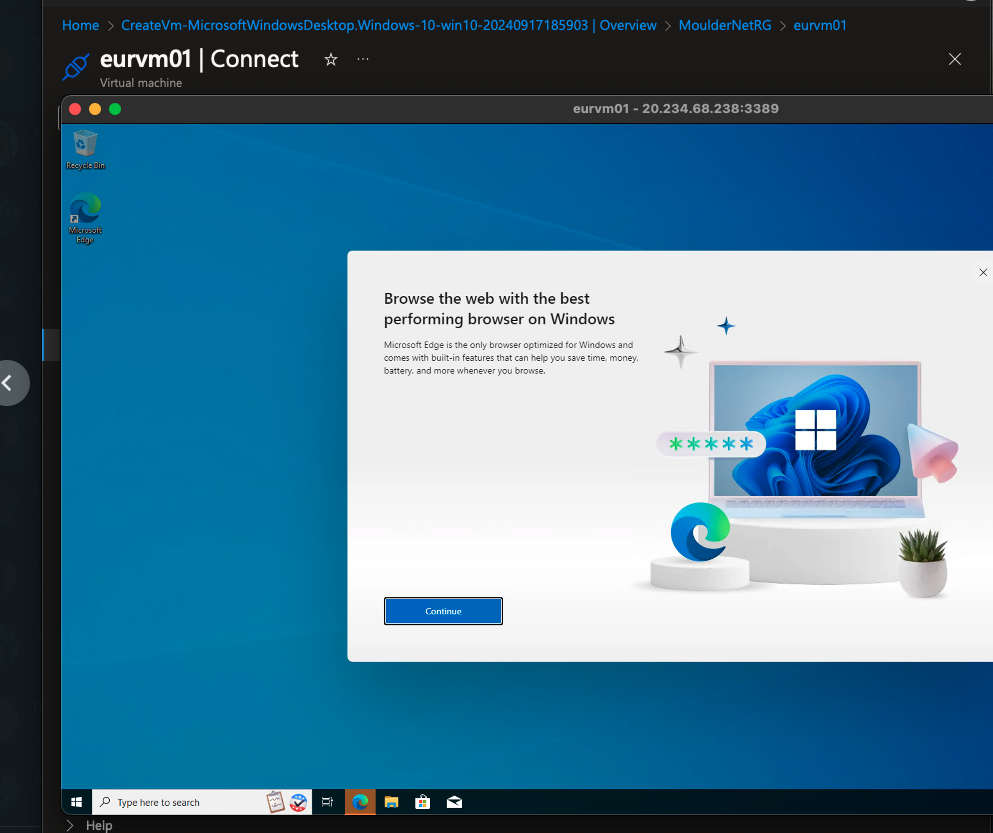
Note that I am able to RDP to this VM given the rules above.
Now I have deleted the RDP rule, which should deny all RDP to the VM.

Now I have a vnet peering between East US(10.1.0.0/24) and North Europe(10.2.0.0/24). North Europe holds the VM I remoted into earlier and East US has a VM that is identical and allows RDP from the internet.

Note the rules on my NSG for eurvm01. It allows RDP and ping from the address space of our peered subnet.

So I will remote into the EUS VM and then remote from there to the EUR VM. First lets ensure it still doesnt work over the internet!

Confirmed. Let’s remote to eusvm01 now.

Confirmed and working. If you are struggling…it’s Windows Firewall. Disable it and it shall work.
To clean up we can simply delete the resource group.

